How do IT asset disposal firms handle data security compliance for laptops
Introduction to IT Asset Disposal and Data Security Compliance
In today's digital age, the secure disposal of IT assets, particularly laptops, is paramount for businesses and individuals alike. With the increasing threat of data breaches and identity theft, IT asset disposal firms must adhere to stringent data security compliance standards. This article will explore how these firms handle data security compliance specifically for laptops, ensuring that sensitive information is protected throughout the disposal process.
The Importance of Data Security Compliance
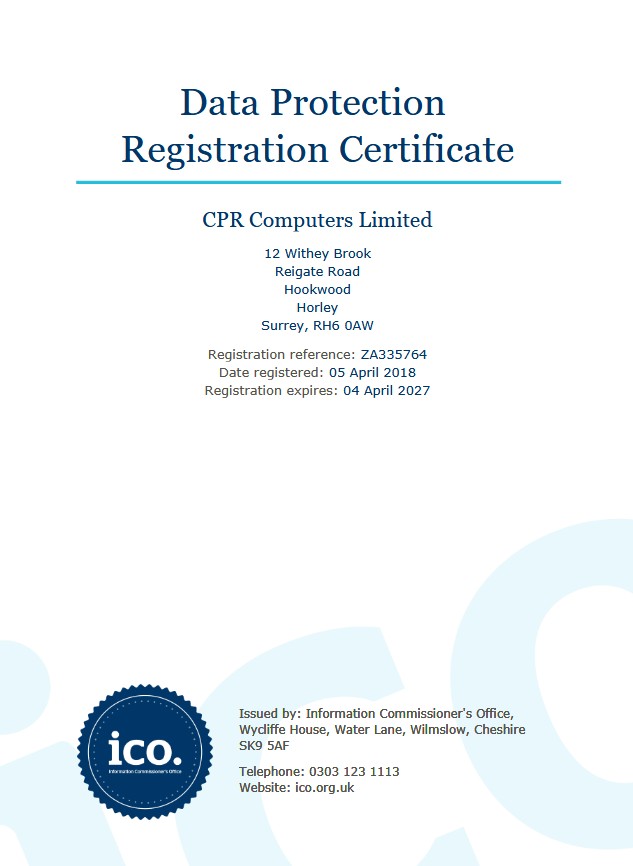
Data security compliance is essential for IT asset disposal firms to mitigate risks associated with data breaches. Compliance with regulations such as GDPR (General Data Protection Regulation) and HIPAA (Health Insurance Portability and Accountability Act) ensures that organizations handle sensitive information responsibly. Failure to comply can result in severe penalties, making it imperative for disposal firms to implement robust data security measures.
Steps Taken by IT Asset Disposal Firms
IT asset disposal firms employ several steps to ensure data security compliance when handling laptops. The process typically begins with a thorough assessment of the devices to determine the best method of data destruction. Following this assessment, firms utilize a combination of physical destruction, software-based data wiping, and secure transportation methods to maintain compliance.

Data Destruction Methods
Two main methods are commonly used for data destruction: software wiping and physical destruction. Software wiping involves overwriting the data multiple times to ensure it cannot be recovered. This method is often certified by reputable organizations, ensuring compliance with industry standards. For firms looking for certified data destruction services, CPR Computer Recycling offers reliable solutions to ensure your laptops are wiped securely.
Physical Destruction of Laptops
In cases where data sensitivity is extremely high, physical destruction is the preferred method. This involves shredding the laptop's hard drive, rendering it completely unusable. Firms like CPR Computer Recycling provide this service to guarantee that no data can be retrieved. Additionally, physical destruction is often accompanied by a certificate of destruction, providing clients with proof of compliance.
Transporting IT Assets Securely
Transporting laptops securely to the disposal facility is another critical aspect of data security compliance. IT asset disposal firms implement secure logistics processes to prevent unauthorized access during transit. This may include locked vehicles and GPS tracking systems. By partnering with trusted companies like CPR Computer Recycling, organizations can ensure their data remains secure from the moment of collection to final disposal.
Documenting the Disposal Process
Documentation is vital to prove compliance with data security regulations. IT asset disposal firms maintain detailed records of the disposal process, including serial numbers, data destruction methods used, and certificates of destruction. This documentation not only helps businesses maintain compliance but also provides reassurance that their data has been handled securely.
Conclusion: Choosing the Right IT Asset Disposal Firm
Selecting an IT asset disposal firm that prioritizes data security compliance is crucial for organizations looking to mitigate risk. Companies like CPR Computer Recycling not only offer reliable data destruction services but also donate profits from recycling efforts to UK charities, making them a socially responsible choice. By ensuring that your old laptops are disposed of securely, you contribute to a safer digital environment while supporting charitable causes.
So, the next time you are ready to do some Computer Recycling, remember. You now have a choice.
Why not Contact Us today and arrange a FREE collection of your old and outdated computer equipment or just use the Online Booking form - Collection Is FREE
Book A Collection Existing Customers
Existing Customers